URGENT UPDATE: Tech enthusiasts are transforming their ROG Ally devices into ROG Enemy systems using the controversial OpenClaw tool, raising significant security concerns. As reported earlier today, users are experimenting with this AI installation despite known vulnerabilities, including a critical remote code execution flaw.
The OpenClaw installation has drawn attention due to its potential to compromise device security, especially when installed on personal devices. Users are warned that this tool should not be used on primary systems and should only be deployed in secure, sandboxed environments. With the popularity of AI applications skyrocketing, the urgency to understand the risks associated with OpenClaw is paramount.
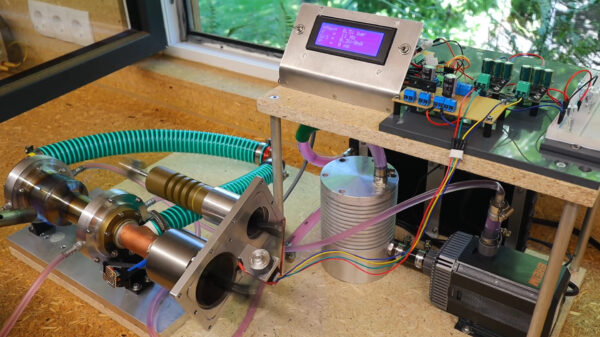
Reports confirm that OpenClaw allows for extensive customization, enabling the installation of various AI models like Mistral and integrations with messaging platforms such as Telegram and WhatsApp. However, these features come with a dark side. The installation process requires disabling critical security settings on Windows 11, exposing devices to potential risks.
The installation journey is fraught with challenges, as users have reported multiple errors, especially when connecting to APIs like Gemini. The need for powerful processing capabilities means that the ROG Ally can only operate effectively within strict power budgets, risking sluggish performance when running advanced AI models. Users have described the process as complex and often overwhelming, leading many to abandon installation attempts altogether.
Despite the hurdles, those who successfully install OpenClaw are greeted by a chaotic AI assistant that prompts users for various tasks, from coding to organizing files. This level of autonomy poses significant risks, as the tool operates outside traditional AI sandboxing protocols. The persistent memory feature, while innovative, raises concerns about data security and privacy.
Furthermore, security experts are urging caution regarding the newly launched skill store, ClawHub. Researchers have already identified numerous malicious skills uploaded to the platform, making it essential for users to audit all installations thoroughly. Experts warn that avoiding installations labeled as “Crypto Ticker” or “Social Media Manager” could prevent potential account takeovers.
The vulnerabilities associated with OpenClaw include the alarming CVE-2026-25253, a one-click exploit that could allow attackers to seize control of devices through simple web access. Though patched, the risk remains high for users who do not implement stringent security measures such as binding the gateway port to local addresses.
As more users engage with OpenClaw, the implications for device security and user data privacy are significant. While the tool pushes the boundaries of AI capabilities, it simultaneously exposes users to unprecedented risks.
WHAT’S NEXT: Users and tech enthusiasts are urged to stay vigilant and consider the potential dangers of installing OpenClaw on their devices. As the conversation around AI security evolves, new developments will continue to emerge. Stay tuned for further updates on this developing story.